WPML is a famous premium multilingual plugin for WordPress.
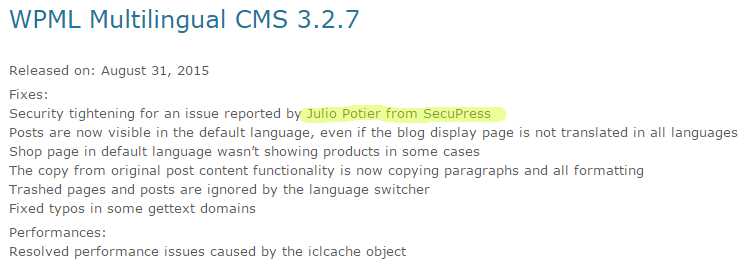
On 08/31/2015 the version 3.2.7 fix a XSS flaw already there since v2.9.3.
The file is ajax.php at plugin’s root, the code is:
The plugin will read the
Accept-Language header, cut it using ;, take the first element, cut it using ,, take the first element again and displays it lowercased.
The flaw is that there is no sanitization o the output, so it’s easy to modify a HTTP request header to insert JS code that will be executed, or even full PHP code that could be included later using a LFI (Local File Inclusion) flaw..
The version 3.2.7 fix the flaw adding sanitization on the ouput.